Cybersecurity Manual
NARUC has developed the Cybersecurity Manual, a comprehensive suite of cybersecurity tools, to help public utility commissions (PUCs) gather and evaluate information from utilities about their cybersecurity risk management and preparedness.
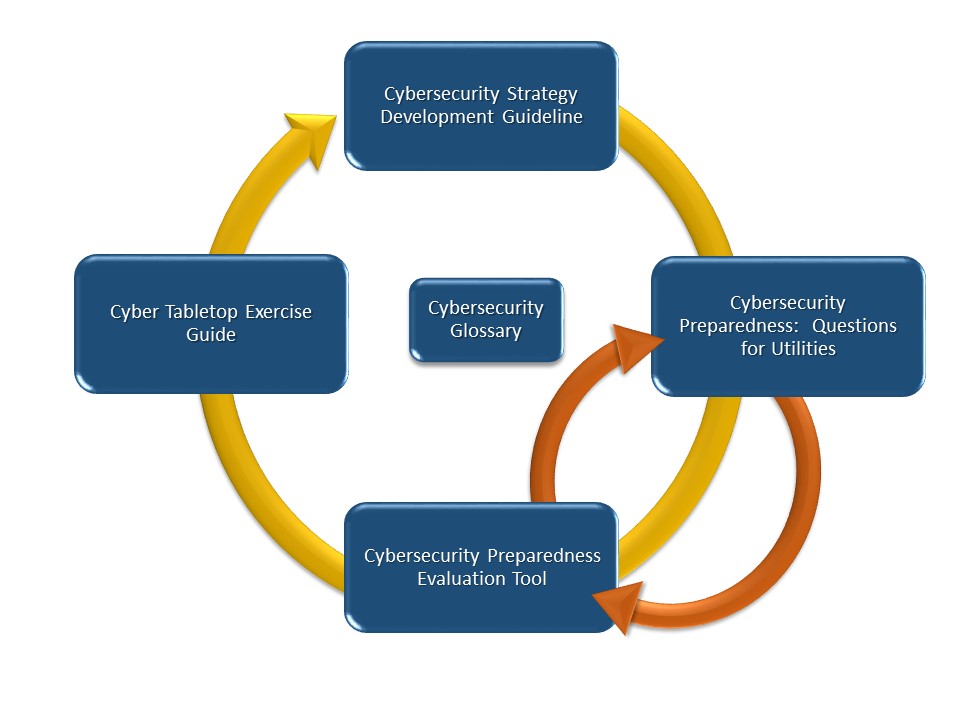
Components of the Cybersecurity Manual can be used individually but are designed to work together. NARUC’s intent is to provide a comprehensive set of assessment tools that, when applied, provide a consistent, complete view of utilities’ cybersecurity preparedness. The diagram below depicts the complementary, process-oriented relationship among these components.
The content of each component in the Cybersecurity Manual is customizable to meet specific goals, objectives, and requirements that PUCs have established around cybersecurity, complementing resources developed by and for utilities and other practitioners. Geared toward non-technical, policy-oriented users, each component captures information in sufficient detail to support PUC decision making.
This document aims to guide commissions’ interactions with their utilities on issues related to cybersecurity, drawing from the experiences of federal, state, and private-sector stakeholders, including state PUCs themselves. Further, it provides guidance and practices for regulators to consider as they develop and implement their strategies. Commissions that have already developed a strategy can use this guide to review and enhance their current strategy. Download
This resource provides a set of comprehensive, context-sensitive questions that PUCs can ask of a utility to gain a detailed understanding of its current cybersecurity risk management program and practices. The questions build upon and add to those included in prior NARUC publications. Download
The CPET provides a structured approach for PUCs to use in assessing the maturity of a utility’s cybersecurity risk management program and gauging capability improvements over time. The CPET is designed to be used with the Questions for Utilities on an iterative basis to help PUCs identify cybersecurity gaps, spur utilities’ adoption of additional mitigation strategies, and inform cybersecurity investment decisions. Download
This guide details the steps that PUCs can take to design, execute, and evaluate a cybersecurity-focused tabletop exercise (TTX). An exercise could examine utilities’ and other stakeholders’ readiness to respond to and recover from a cybersecurity incident or analyze the PUC’s internal capabilities. This guide includes example scenarios and customizable templates. Download
This glossary contains cybersecurity terms used throughout the Cybersecurity Manual, as well as “terms of art” that utilities may use during discussions with PUCs. It also contains a list of icybersecurity related events that demonstrate the growing threats and vulnerabilities against critical infrastructure sectors. Open